So you’re SSHing to your remote server and you noticed there were thousands of failed attempts to get into your server since your last login. What can you do about it? Well, you can use a SSH key and disable password login. You can also use a different port to make it a bit more difficult for hackers and script-kiddies to find the SSH port.
If you run this command, you can see all the failed attempts on your server including their IP addresses, the username they used, port number and when they tried it.
For CentOS / RHEL servers
grep "Failed password" /var/log/secureFor Ubuntu servers
grep "Failed password" /var/log/auth.log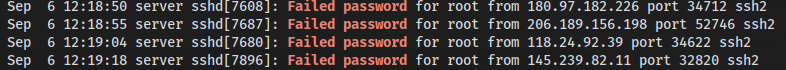
Thanks to tecmint for sharing this.
satta king 786
October 2, 2020 — 3:38 am
Hello, i think that i noticed you visited my blog thus i
came to return the choose?.I’m trying to in finding things
to enhance my web site!I assume its good enough to use some of your
ideas!!